Apps on Instagram can be a great benefit to anyone looking to grow their profile, get more out of the social network, or even just change the way it looks and functions.
Great, high quality apps for a site like Instagram can bring a lot of features to your fingertips. For example:
- Hootsuite brings all of your social media dashboards into one combined feed, where you can manage your total social presence instead of several fragmented presences across different sites.
- Sprinklr brings combined social listening, engagement, advertising, and advocacy to an enterprise-level platform.
- HYP3R helps with customer engagement on social media by focusing primarily on local and hyper-local marketing techniques.
- Later allows you to schedule posts and plan out an editorial calendar weeks or months in advance.
These are all excellent, vetted, high quality apps. You have to pay for them as platforms, but the power you get from them is unparalleled. They’re officially endorsed by Facebook/Instagram, too, as you can see by browsing their list of official Instagram Marketing Partners.
When you want Instagram apps to bring you new features, but you don’t want to pay for them, you often turn to smaller brands and apps you may not have heard of before. They aren’t on the official list, they aren’t badged or vetted, they’re just apps someone has developed.
The problem with this is that so many of these apps are, well, dangerous. They’re shady. They exist to provide some semblance of value, while they enact their own agendas in the background. They’re basically like viruses for your social profiles rather than your computer.
Authorization Versus OAuth
There are two ways an app can be authorized to use your account. The first is to authorize it manually, by logging in through the app. In other words, you open up the app and give it your username and password.
This obviously has some issues. You’re giving your login information to a third party, and you have no idea what they’re going to do with it. Sure, some of them will just use it to log into Instagram to do whatever they claim to do. Others will be a lot more nefarious with it. They might use your profile in ways you don’t want them to, by following or unfollowing people, commenting in ways you might not want, and who knows what else. Others could even just take your information and sell it as part of a bundle of hacked names/passwords, or try to hack other profiles you might control with the same information.
The tricky part is that, due to Instagram’s own decisions, this is not only very common but often trusted. See, up until very recently, Instagram didn’t have a way to schedule posts. A lot of third party services offered post scheduling, but in order to do so, they needed your information. They didn’t actually automate anything; rather, they just had a bank of devices, each logged into a different profile, with timers set and posts ready to be posted.
In order for those services to work, they needed access to your account. Since the other method – which I’ll discuss next – didn’t allow posting, they needed to log in as you, so they needed your information. This conditioned users to give over their sensitive information, regardless of whether or not they trusted the tool.
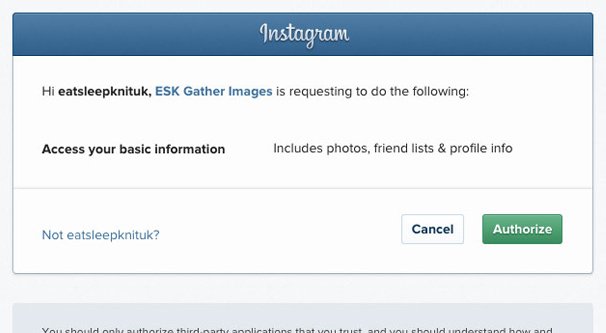
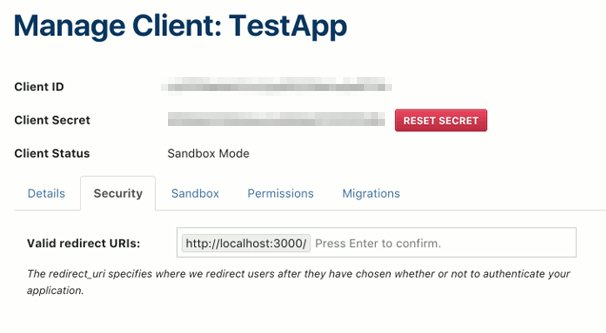
The other way to authorize an app is using OAuth, or Open Authorization. OAuth is a token-based protocol that a third party app can use to gain access to certain limited features of your profile without needing to see your username or password directly.
The way it works is pretty simple. You want to use an app that uses OAuth. The app sees your request and asks for OAuth. You log in using your username and password into the Instagram OAuth menu, which generates a token unique to this authentication. The token is handed over to the app, which can use it to access those account features. The app never sees your information, just the token. No other app can use that specific token, and the token can be easily revoked if necessary, without you needing to change your account information.
OAuth isn’t perfectly safe, however. The OAuth token allows the app to take over certain account features, like follows, unfollows, and recently the ability to post, with Instagram’s API updates. As you’ll see below, even legitimate access can cause you trouble if that access is used for nefarious deeds.
Checking Authorized Apps
If you’ve ever logged into Instagram using a third party app, you may want to check what is and isn’t still authorized. Some apps deliberately de-authorize themselves after a long enough period of inactivity, while others will cling to your profile indefinitely.
I highly recommend that everyone reading this checks what apps are authorized on their profiles. If you see something you don’t recognize, Google it and see if it’s something you’re using, something you’ve used in the past, or something you didn’t authorize but has wormed its way into your profile regardless.
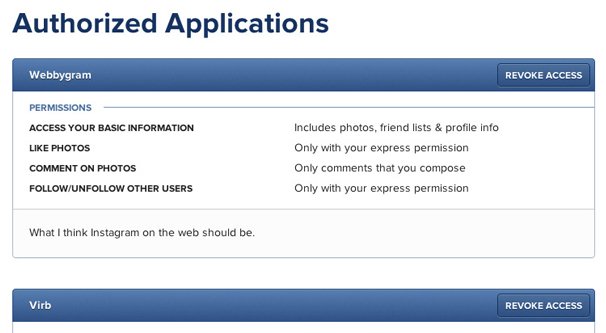
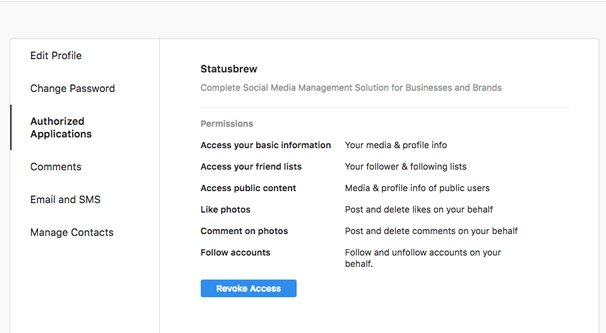
In order to check, you need to log in to Instagram. From your profile page, click on the settings wheel, and then “Authorized Apps.” This will show you a list of all of the apps that have access to your account, as well as what permissions it has.
Different levels of permissions mean different things. The least impactful is “access your basic information.” This just allows the app to see what you post and to access your bio, username, follower count, and other basic public info. Apps with this level of permissions aren’t really able to hurt your account, but they can scrape your personal information if they want.
Other levels of permissions have other features. They might be able to access your follower list and be able to follow new accounts or unfollow previously followed accounts. They might be able to see your likes and like new content. They might be able to leave comments. Some can even post for you, though these generally need to be authorized marketing partners, and are thus vetted for their behavior.
In any case, look over the apps you have authorized to your account. If no apps appear on the list, you may have authorized something using your username and password. This list is only for official apps that have used your OAuth access token to link to your account.
Feel free to remove any app you’re not sure about. If you revoke access to an app you use, the next time you go to use it, you will need to re-authenticate it, but the worst that can happen is you lose a scheduled post or miss a bit of analytics data.
If you think you’ve given your password to an “app” that doesn’t use OAuth, change your password. Changing your password does not revoke authorization from OAuth apps, but it will prevent anyone else from logging in naturally using your information.
Any time you’re considering using an app for a task, ask yourself if it’s something you really need the app to do. Then ask yourself if the app is vetted and trustworthy. Don’t just assume an app is good based on reviews, since reviews can be faked.
Any time you install an app, likewise, monitor your account for any potential damages. Check to see if you’re leaving comments you don’t want to be leaving, if you’re following accounts you don’t want to be following, or otherwise taking actions you don’t want to be taking. Give each app a trial period where you keep an eye on it to make sure it doesn’t do anything it shouldn’t. Only then can you consider the app safe enough to really use.
The Damage Bad Apps Can Do
So what’s the problem, anyway? What can a bad app really do to your account? Well, depending on how malicious it is, it can do a lot.
The first and least dangerous thing a bad app can do is scrape your personal information. Since this is all public to begin with, it’s not really a dangerous effect, though it certainly makes it easier for spammers to know more about you.
Stepping up the scale, bad apps can mess with your followers and who you’re following. In fact, this is actually a selling point for many of them. Apps that claim to audit your followers to allow you to:
- Follow new accounts in your niche.
- Stop following accounts that don’t follow you.
- Stop following accounts that haven’t posted in 6+ months.
- Remove bot followers.
…and so on, these are all potentially good or potentially bad. There’s nothing wrong with blocking bots or removing follows you don’t want. The problem comes when these apps have their own agenda. It’s one thing to remove the follow from someone who is inactive. It’s quite another to then follow everyone who the bot owner decides they want you to follow. You essentially become part of a botnet. All those sites that sell 10,000 followers in a day or whatever? Those are using compromised apps like these to follow you.
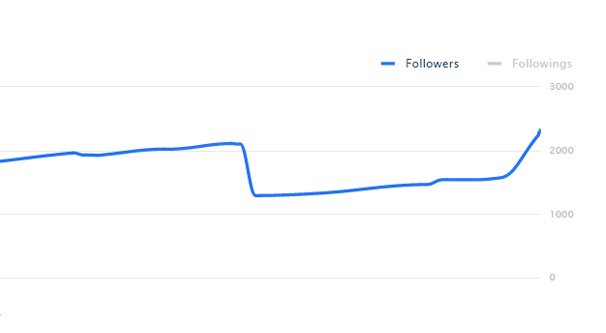
Basically, you run the risk of encountering Instagram’s bot detection, looking for aggressive follower churn. The “follow/unfollow method” is promoted by a lot of shady companies as effective “if you don’t over-do it”, but it’s still a technique explicitly labeled a bannable offense in the Instagram terms of use. These kinds of bots can get your account temporarily blocked or permanently banned, depending on the scale of the issue and if you keep going back to it.
Of course, you also ruin your own feed. When an app follows 5,000 accounts you don’t care about, your organic feed becomes nigh-unusable. If you were using Instagram as a curated feed of content or to keep track of people you wanted to follow, well, so much for that.
Authorized apps with devious purposes can do more than just mess with your followers, they can mess with your engagement. They can’t make posts for you, but they can reply or leave comments on other pieces of content. In fact, many of them go out of their way to leave basic bot-like comments on whatever posts the app author wants to promote. Again, this is probably a side business for the app owner; they sell the engagement.
Of course, when your account is one of thousands leaving the same sort of comments on the same set of profiles, it’s easy for Instagram to decide you’re a bot account and ban you.
Authorized apps can also run afoul of the various possible actions that lead to the dreaded Instagram shadowban. While it’s possible to recover from a shadowban, it’s still annoying, and it hurts your growth for weeks or months afterwards.
What it all really comes down to is that these apps, when authorized to use your account, can use your account in ways you don’t necessarily want them to. Good apps, of course, let you control what’s happening. Other apps let you automate based on certain rules, which can run afoul of the Instagram terms if you don’t know what you’re doing with them. Yet others exist solely to pretend they provide a service, while using your account to do what they want.